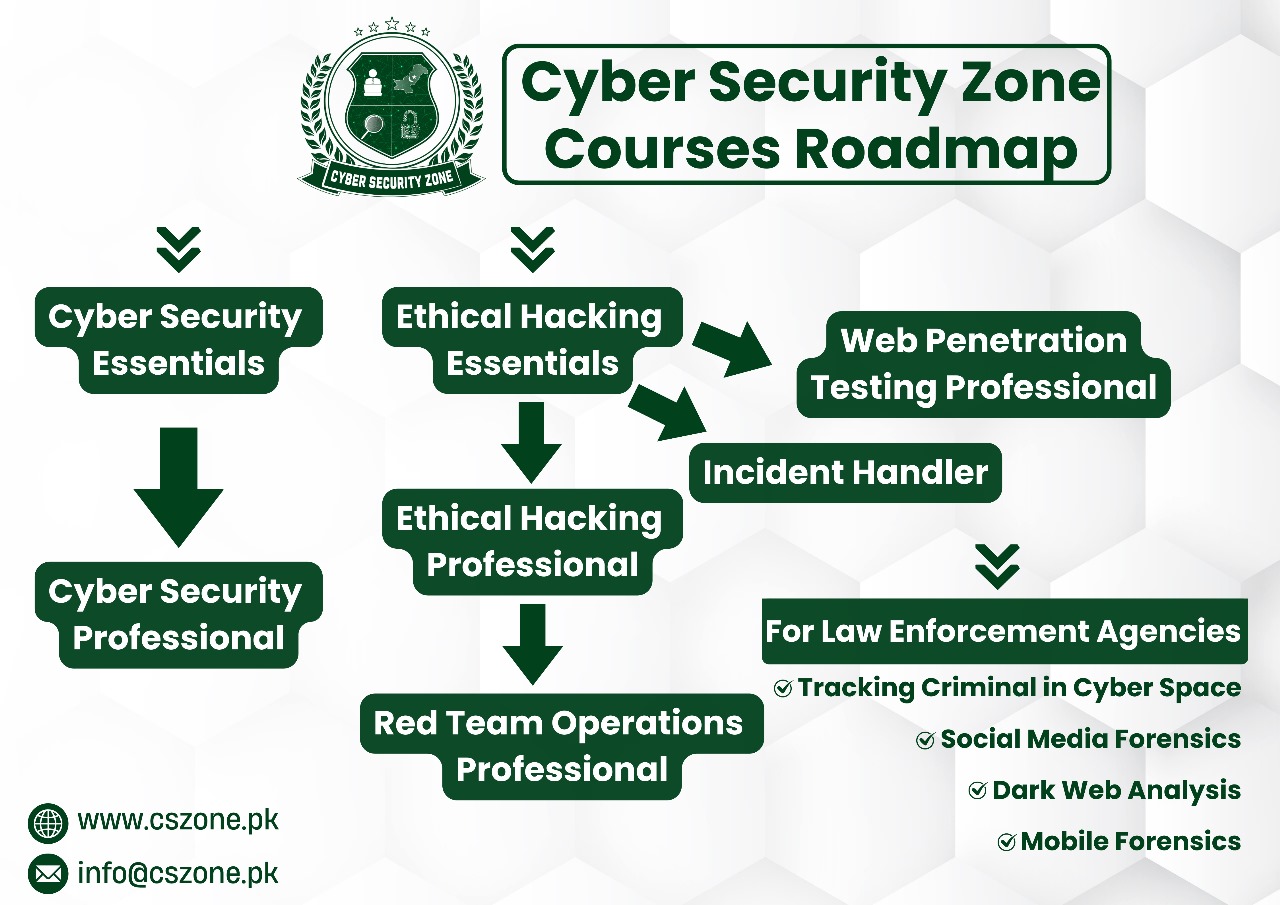
Cyber Security Essentials by Cyber Security Zone is designed to equip beginners with the foundational knowledge and skills needed to embark on a career in cyber security. This course covers the basic concepts, tools, and practices that are critical for safeguarding information and assets in the digital world. Through interactive learning modules, practical exercises, and real-world scenarios, students will learn how to identify potential threats, protect against cyber attacks, and understand the importance of cyber security in today’s technology-driven society.
Target Audience: Fresh students wanting to start a career in cybersecurity.